How to Use Email Breach Data in Credit Scoring
Learn how lenders use email breach data to assess risk, detect fraud, and make faster, more accurate credit decisions.
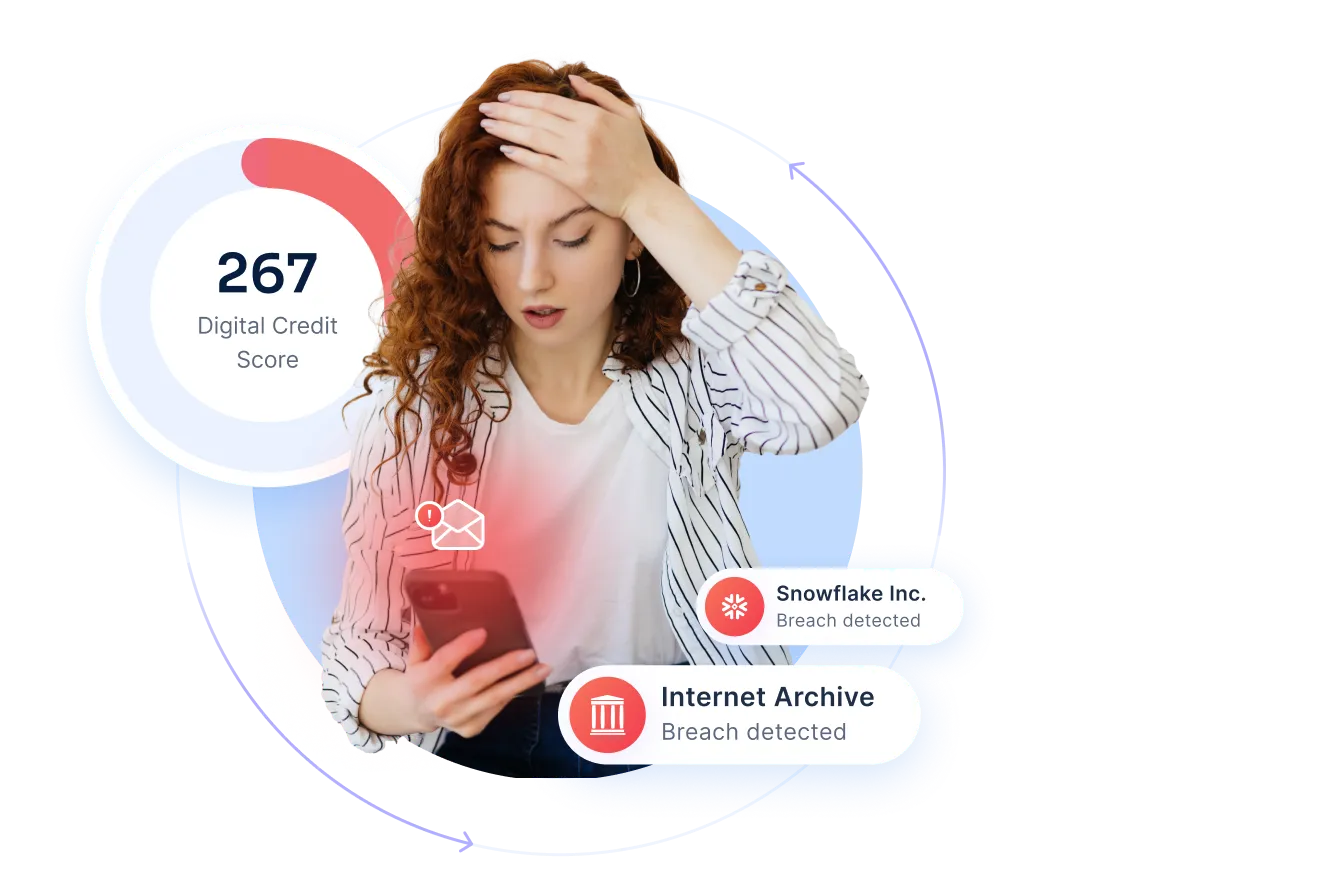
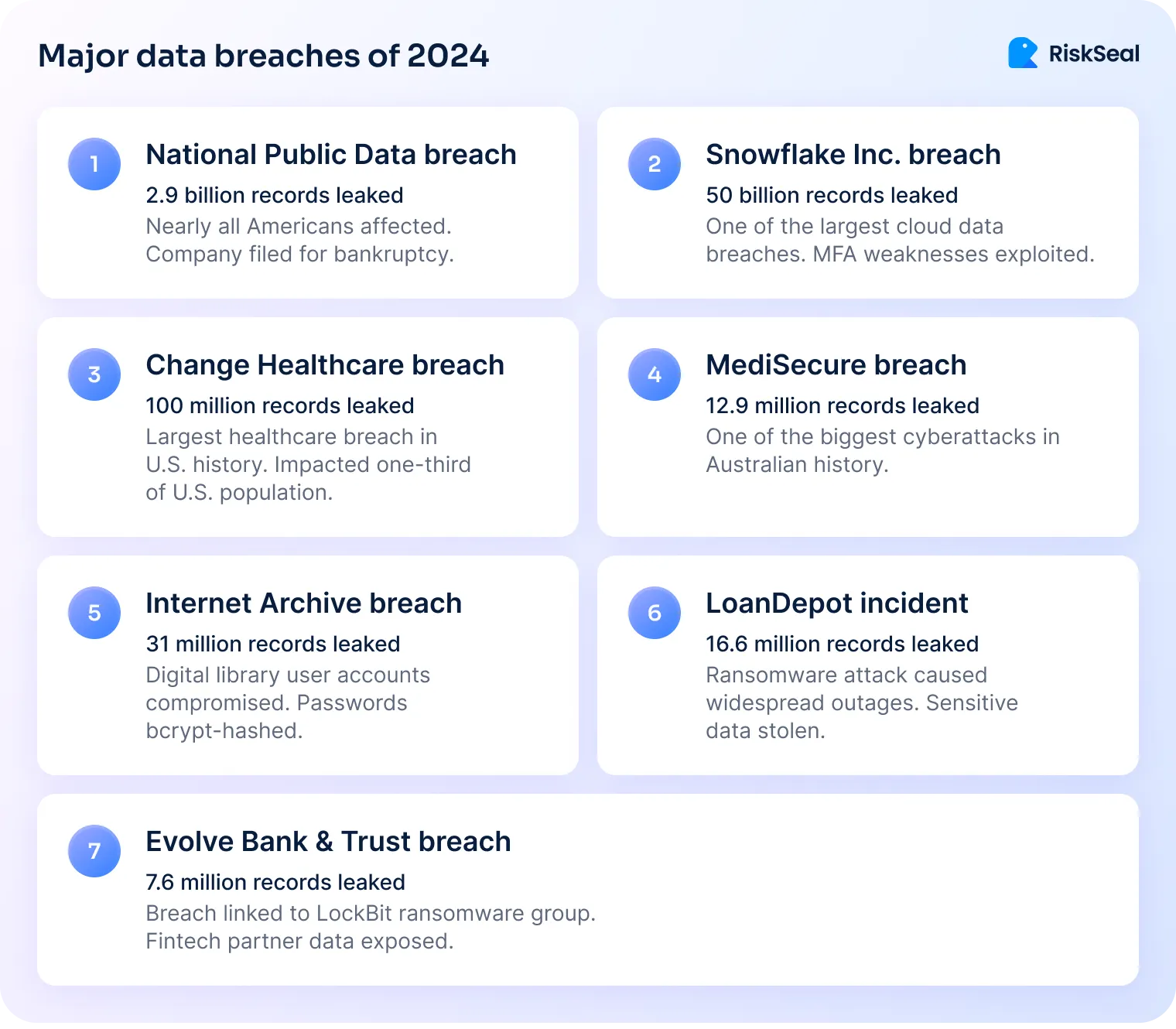
In 2024, over 5.5 billion accounts were compromised, nearly eight times more than in 2023.
That’s roughly 180 accounts breached every second. Often exposing names, phone numbers, and other sensitive details.
This surge is more than a cybersecurity headline for lenders and risk teams. It’s a rich, underused source of signals for identity verification, fraud detection, and smarter credit scoring.
What is email breach data?
Email breach data shows that an email address was part of a known data leak. A breach happens when hackers access information from a website, app, or online service.
For credit and risk assessment, the most useful parts are when, where, and how many times a data breach happened to a certain email.
There are several types of breaches:
Ethical providers collect this data from trusted sources. They never store passwords or personal content from the breach.
Instead, they keep only metadata, like breach dates and domain names. This gives lenders and risk teams valuable identity and risk signals while protecting sensitive information.
5 digital maturity signals lenders should track
These are the key signs lenders can look for when assessing a borrower’s digital maturity.
1. Email account age
An older email address often points to a stable, long-term digital presence. If you can estimate the age of an email account and find that it has existed for many years, it suggests the borrower has a consistent online identity.
2. Breach history timing
Emails appearing in older breaches can indicate active use over time. This isn’t negative by itself. Older breaches may confirm the account has been in continuous use for years.
3. Activity across platforms
An email linked to multiple reputable platforms (e.g., banking, shopping, social media) shows digital engagement and a traceable history. This helps confirm the person is who they claim to be.
4. Absence of suspicious patterns
Brand-new emails with no breach history may seem “clean” but can be a risk. They’re sometimes created for synthetic identities, bots, or short-term fraudulent activity.
5. Consistency in usage
When the same email appears across different data sources and timeframes, it signals reliability. Inconsistent records or gaps in history may need closer review.
3 practical use cases for email risk assessment in lending
Email breach data can be valuable in different stages of the lending process. It helps confirm identity, fill data gaps, and improve risk models.
For example, an email created in 2010, active on multiple major platforms, and present in an old breach shows high digital maturity.
By contrast, an account created only two weeks before an application, with no associated activity, can be a red flag.
Here are three practical ways lenders can use it.
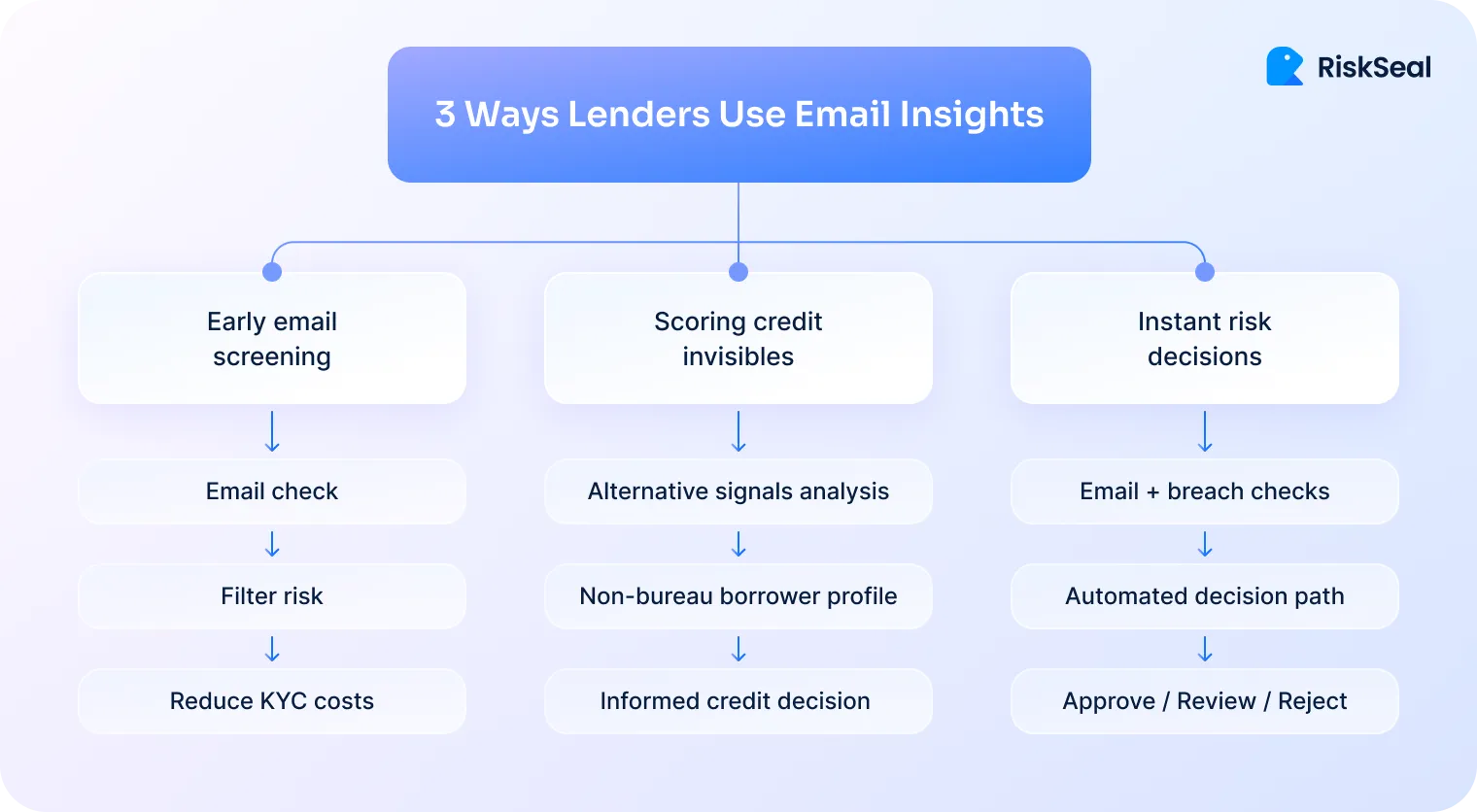
#1. Onboarding and pre-KYC
Every loan application includes an email address. Until recently, this detail was almost completely overlooked in credit risk checks.
Running an email breach history check at the very start of the process can make a big difference.
It allows lenders to filter out suspicious applications before moving into costly, time-consuming KYC procedures.
Combined with other identifiers, this early signal helps flag applicants with inconsistent or unusual digital footprints.
As a result, fewer bad actors make it deeper into the system, and operational costs stay lower.
#2. Thin-file borrowers scoring
Some borrowers lack a traditional credit history or enough bureau data to score accurately.
Email breach metadata, along with email address checks for the thin-file applicants, can provide useful context.
For instance, a borrower with a long-standing, active email address may still be a good credit risk. Even without bureau records.
Using these signals can help lenders approve more “invisible prime” customers and keep default rates under control.
#3. Real-time risk modeling
Integrating breach data directly into scoring engines allows for instant decision-making. Lenders can create automated rules based on breach history and email age.
For example, if an email is less than six months old and has no breach record, the application might be sent for manual review.
These rules make it easier to spot suspicious applications without slowing down approvals for legitimate customers.
It’s not about rejecting every “clean” email, but about adding context to make smarter, faster credit decisions.
How to implement email address risk scoring in credit workflows
Email breach data works best when it’s part of a lender’s existing credit risk process.
With the right setup, it can deliver instant insights without slowing down approvals.
Here’s how it fits into real workflows.
1. API integration
An API-driven email lookup lets lenders check breach data the moment an application comes in. It runs automatically in the background, so there’s no extra step for the applicant.
The process integrates easily into onboarding flows, CRM systems, and loan origination platforms.
This means lenders can act on breach intelligence in real time. Without manual checks or delays.
2. Interpreting email insights breach data
A breach “hit” doesn’t always mean high risk. Older breaches can signal digital maturity, showing the borrower has had the same email for years.
When reviewing breach data, lenders should consider three main factors:
1. Number of breaches. Numerous recent breaches could mean a higher risk.
2. Date of first breach. An older breach suggests a longer history and a stable identity.
3. Domains affected. Breaches from major, reputable platforms may be neutral compared to those from risky sites.
By weighing these factors, lenders can avoid false positives and make more balanced decisions.
3. Combining signals
Breach data becomes even more powerful when combined with other digital identity checks:
- Phone lookup helps verify if a borrower’s number is active. It also cross-references the number with social accounts or suspicious patterns, in a way similar to device fingerprinting tools.
- Email lookup analyzes deliverability, linked accounts, and hidden addresses, similar to what an email reverse lookup tool reveals. This is giving lenders a fuller view of identity.
- IP lookup validates the true origin of a connection and flags mismatches between an applicant’s claimed and actual location. It also exposes VPN, proxy, or TOR usage.
Together, these tools create a complete digital footprint that’s much harder for fraudsters to fake.
With smart integration, email analysis for credit risk can turn breach data from a simple fact into a reliable tool.
Case studies on email breach data in action
These examples come from real lender experiences, with names and some details changed for privacy.
They show how breach data, when read in context, helps lenders make better decisions.
Case #1. High digital maturity
A borrower applies for a loan with a Gmail account created 12 years ago. The first recorded breach was in 2014, and the account remains active.
This history shows a stable, long-term digital presence.
The old breach is not a negative factor here. It actually confirms continuous use.
The lender approves the application with standard monitoring, confident in the borrower’s identity stability.
Case #2. Potential synthetic identity
An applicant submits a Yahoo account created just two weeks before the application.
The account has no breach history and no signs of long-term activity.

On the surface, this looks “clean,” but it could be a newly created identity for fraudulent purposes.
The lender flags the case for manual KYC review to confirm the applicant’s legitimacy before proceeding.
Case #3. Behavioral risk profile
A borrower applies using an account with multiple breaches in the last six months. All breaches are from gaming and gambling platforms.
While the account itself is not brand new, the nature of these recent breaches suggests potentially riskier financial behavior.
The lender chooses to adjust the credit limit or offer a secured product instead of rejecting outright.
These cases show that breach data is most valuable when considered with context. It’s not about penalizing every breach. But about understanding what the timing, source, and activity reveal about a borrower’s identity and risk profile.
How to use email risk assessment tools ethically and legally
Using email breach data in credit risk assessments requires strict adherence to privacy and security standards.
The key principles include:
- Follow regulations. GDPR and local laws allow only breach metadata to be used.
- Gain consent and ensure transparency. Inform applicants that digital identity checks are part of the onboarding process.
- Apply data minimization. Store only the necessary indicators – breach date, domain, and count. Do not store exposed credentials or personal data.
- Ensure strong security standards. Use robust encryption, secure storage, and strict access controls to safeguard breach data.
These principles provide valuable identity and risk signals while protecting the privacy and security of applicants.
RiskSeal holds ISO/IEC 27001:2022 certification, confirming internationally recognized data protection measures.
How RiskSeal turns email breach data into actionable insights
RiskSeal turns breach metadata into clear signals for credit decisions.
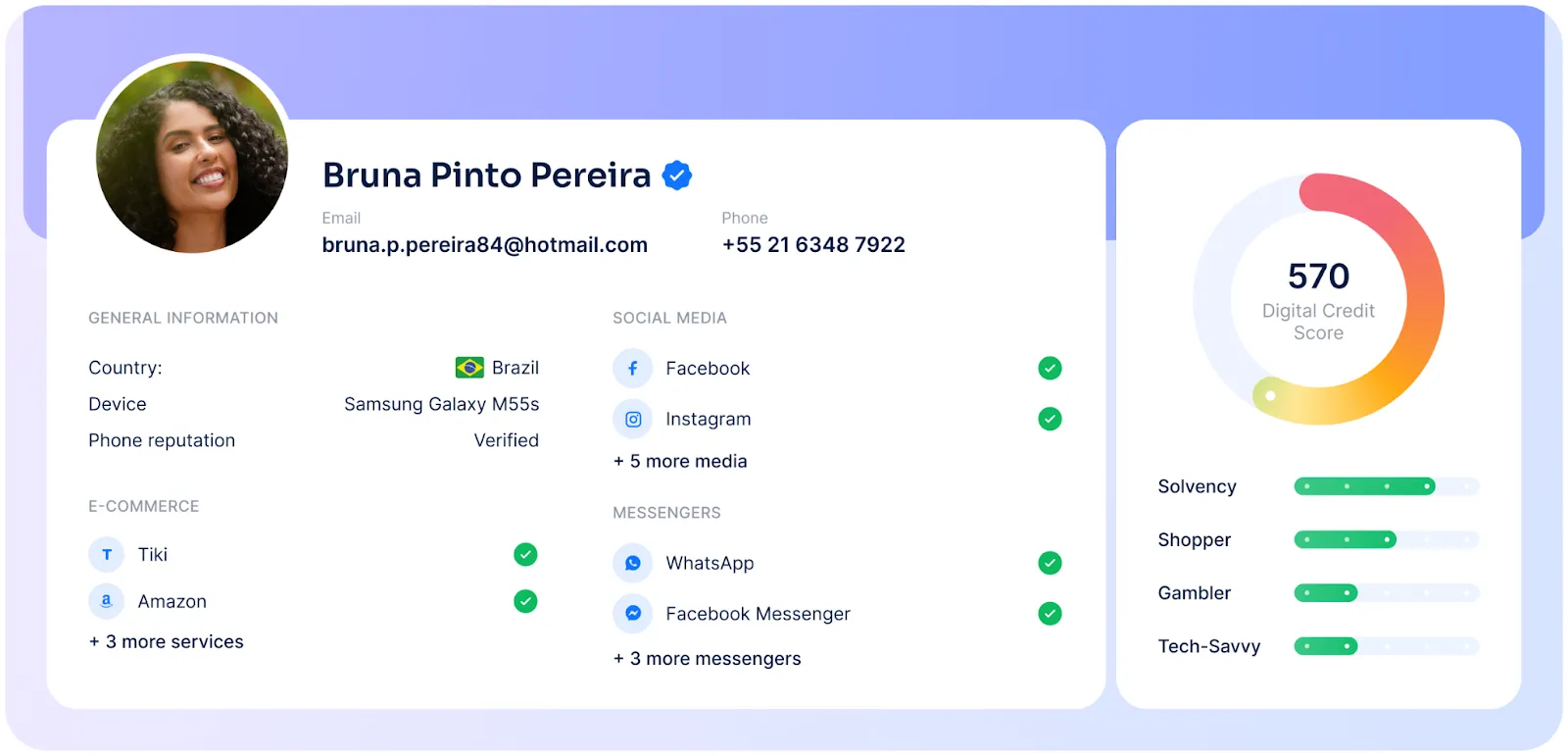
It blends breach history with phone, device, behavioral, and other alternative data to give a complete view of each applicant.
Data enrichment
With a single API call, RiskSeal checks deliverability, social and digital profiles, domain details, and breach history. It also identifies creation dates, disposable domains, and spam-listed addresses.
This process provides more than 400 unique data points, giving lenders deep context about an applicant’s digital footprint.
AI-driven analytics
RiskSeal’s scoring engine factors in digital maturity signals from breach data.
It analyzes the timing, number, and source of breaches alongside other behavioral indicators.
This real-time scoring helps lenders approve strong applicants faster while flagging suspicious cases for review.
Explainable outcomes
Every breach-related decision is backed by clear reasoning.
RiskSeal shows why a profile was flagged or approved, ensuring full transparency and compliance.
Lenders can see exactly how breach data influenced the decision.
Flexible integration
RiskSeal fits easily into existing credit workflows.
Lenders can connect via API for real-time checks, run batch uploads for portfolio reviews, or integrate with CRM tools for ongoing monitoring.
Email address risk scoring software to enhance lending decisions
RiskSeal enriches applicant profiles with verified breach intelligence.
Combined with other digital signals, this helps lenders improve approval accuracy, reduce fraud risk, and run operations more efficiently.
All without slowing down the customer journey.
Key takeaways on email address lookup and breach data
Email breach data is a powerful yet underused trust signal in credit risk assessment.
It helps lenders confirm identities during onboarding, approve more thin-file borrowers, and detect potential fraud early.
The value lies in context. Breach history should always be evaluated alongside other digital footprint signals like account age, platform activity, and device data.
With RiskSeal, lenders get a scalable, compliant email lookup solution.
It fits seamlessly into existing workflows and improves approval accuracy. All without adding friction to the customer journey.

The 2026 guide to LATAM digital footprints for credit scoring
Inside the LATAM alternative credit data report





FAQ
See more
Learn how IP address analysis can enhance borrower creditworthiness assessments.

Discover how AI is changing credit scoring with real-time data, boosting accuracy, reducing risk, and improving financial inclusivity.

Discover and debunk six common misconceptions about AI in credit scoring and see how RiskSeal helps modern lenders leverage AI safely and effectively.


.svg)

.webp)