The Role of IP Address Analysis in Credit Risk Assessment
Explore how IP address analysis improves credit risk assessment, detects fraud, and reduces loan defaults.

Lending to unreliable borrowers costs banks billions of dollars annually. One reason for this situation is the flaws in traditional credit risk management.
Looking for a way to improve the quality of your loan portfolio and reduce default rates? This article will show you how IP address analysis can help.
Why IP analysis matters in credit risk management
In recent years, the number of loans taken out by criminals has increased sharply. For example, financial losses from credit card fraud are projected to exceed $43 billion as early as 2026:
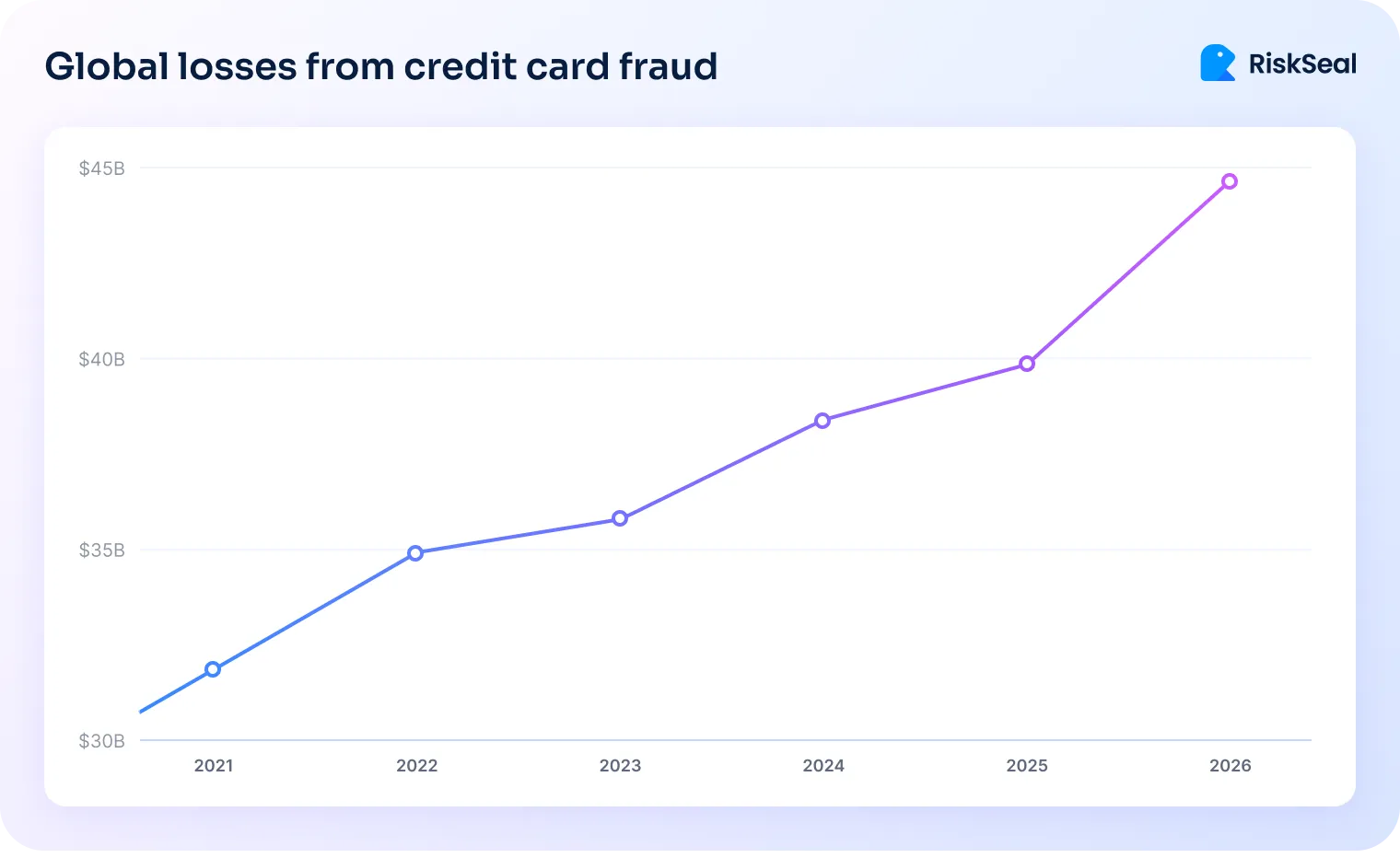
The global nature of financial fraud is further demonstrated by another statistic.
In the U.S., 25% of banks and fintech companies report annual losses exceeding $1 billion due to criminal activities:

Such a trend is partly explained by the shortcomings of traditional credit scoring. These include a limited set of data used (the borrower's credit history) and numerous opportunities for falsifying information.
The use of VPNs, proxy servers, and other anonymizers has been growing recently. Statistics show that 1.3 billion people use VPNs, which accounts for 31% of all internet users.
Understanding this, lenders are increasingly turning to AI credit scoring. In addition to traditional credit bureau data, it takes into account alternative consumer data, including IP address data.
With this information at their disposal, credit organizations can learn a lot about an applicant, including detecting attempts to conceal their real IP address.
Types of fraud based on IP address concealment
Criminals often hide their IP addresses to engage in illegal activities. This allows them to remain anonymous online and avoid exposure.
Common fraud schemes based on IP address concealment include:
#1. Loan stacking
This scheme involves fraudsters simultaneously or within a short time applying for loans from multiple credit organizations.
Their goal is to take out as many loans as possible without lenders realizing they already have significant debt.
To achieve this, fraudsters often manipulate their data, including masking their IP.
This creates the illusion that applications are being submitted from different regions.
#2. Synthetic identities
This type of fraud involves combining real and fabricated information to create a non-existent identity.
For example, fraudsters may use a real Social Security number along with a fake address and phone number.
At the same time, VPNs, proxy servers, or similar services are used to mask the real location.
It is worth noting that this is one of the most widespread types of fraud in the financial sector.
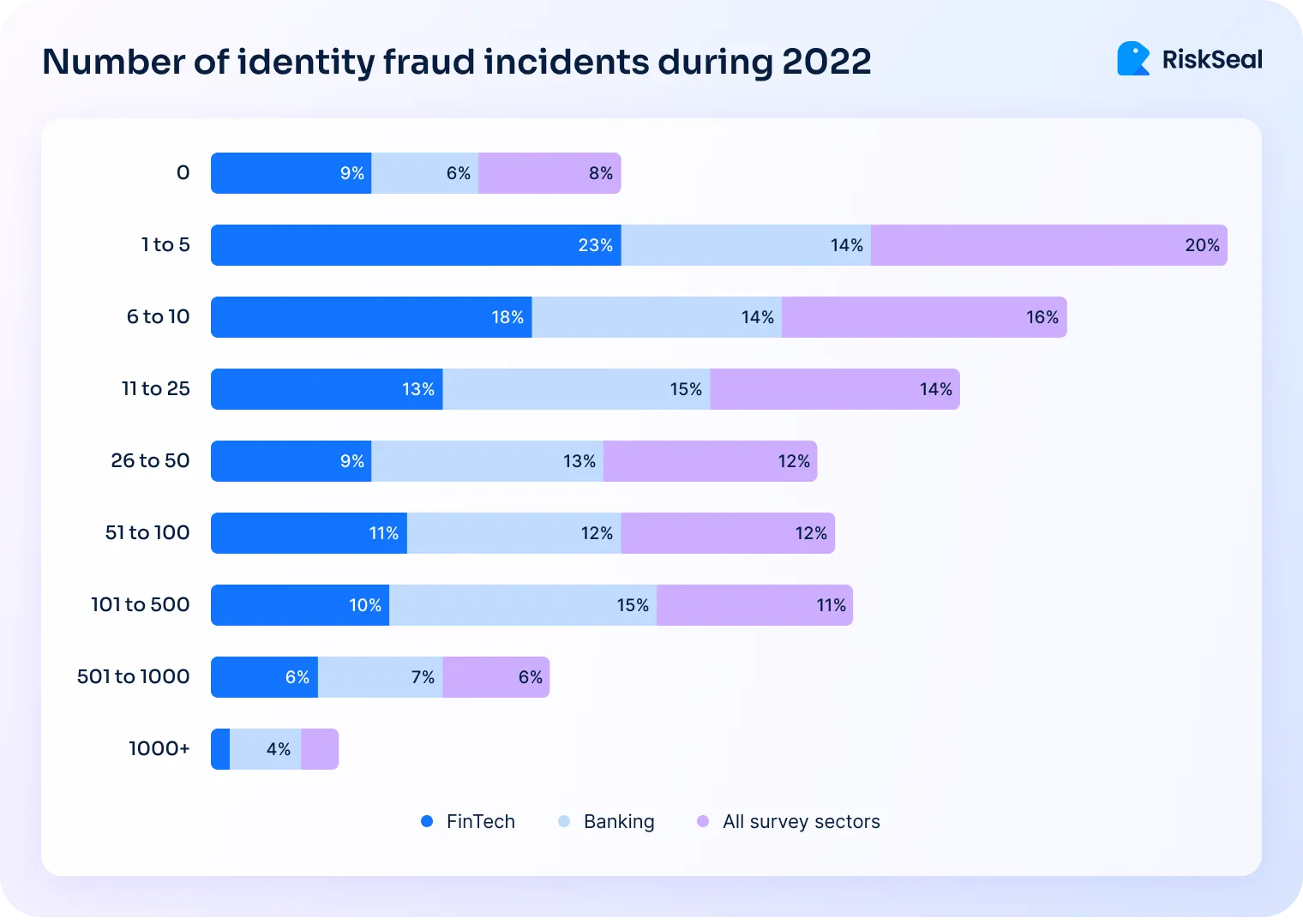
Statistics show that 90% of companies encounter it, with many credit organizations facing dozens or even hundreds of attacks annually:
#3. Chargeback fraud
In this case, a fraudster makes a purchase using a credit card and then files a claim with the bank to request a refund. The most common argument is an unauthorized transaction.
In chargeback fraud, criminals hide their real IP addresses to avoid detection.
Understanding IP address-based risk indicators
What are the capabilities of IP risk assessment in credit risk scoring? By knowing a potential borrower’s IP address, a lender can gain valuable information, such as:
- Geolocation mismatch. A borrower may claim to be in one country while using an IP address from another.

- Use of anonymizers. Attempts to hide a real address using VPNs, TOR, proxies, and similar services are suspicious in themselves.
- Type of IP address (datacenter or residential IPs). According to statistics, 48% of fraudulent traffic comes from residential IPs. Detecting such activity is a red flag for lenders.
- High-risk ISP patterns. If a lender detects an IP address linked to past fraud cases, the applicant is automatically marked as suspicious.
How fraudsters manipulate IPs to evade detection
Fraudsters most commonly use the following services to manipulate IP addresses:
- Proxy servers. Used to route traffic through different IP addresses.
- VPN. What is a VPN? This abbreviation stands for “Virtual Private Network.” It is another method for masking a real IP address.
- TOR network. A tool that routes traffic through multiple servers, making it harder to track users.
Methods of using anonymizers for illegal purposes
Using these services, criminals can execute various fraudulent schemes, such as the following:
1. Multi-accounting and identity fraud using proxies
Multi-accounting is a scheme where fraudsters create multiple accounts on the same platform.
To prevent their IP addresses from being detected, fraudsters use proxy servers. This allows each account to have a different IP address.
Connecting through a proxy helps avoid exposure when using falsified information. This makes it easier to conceal the fraudster’s true identity and real location.
2. Masking stolen credit card transactions with geolocation spoofing
Fraudsters often use stolen credit card data to make illegal transactions.
Using a VPN, proxy, or similar service allows them to make these transactions appear legitimate.
For example, financial institutions often flag a mismatch between the cardholder’s address and the transaction location as a red flag. By changing the visible location of their internet connection, fraudsters can conceal this discrepancy.
3. Use of botnets and malware-infected residential proxies
A botnet is a network of devices that fraudsters can control remotely. Such networks are used for large-scale fraudulent operations.
Botnets are often linked to residential proxies. This makes it harder to track attacks since they create the illusion that the activity is coming from real users.
Top 5 techniques to detect suspicious IPs
There are several methods for detecting suspicious IP addresses.

#1. Identifying anonymized traffic
This is possible by detecting connections via VPNs, TOR, or proxies.
This practice is successfully implemented by the RiskSeal scoring system, which specializes in credit risk assessment with digital footprint analysis.
As part of this analysis, the platform performs an IP location lookup. This method helps detect anonymizers and alerts lenders to such applicants.
#2. WebRTC and DNS leak tests
WebRTC is a browser feature that finds the best route for communication between two peer nodes. It can reveal a user’s real IP address even if they are using a VPN.
DNS (Domain Name System) is responsible for converting domain names into IP addresses.
If DNS queries are routed through an ISP’s servers instead of a VPN, a DNS leak occurs, exposing the user’s real IP address.
#3. Latency and Ping tests
These methods measure connection speed and can help identify suspicious IP addresses.
For example, watch for long delays (which may mean traffic from suspicious sources) and strange routing (which could indicate an attempt to hide the real location).
#4. Browser vs. Timezone inconsistencies
Any mismatch in user data is suspicious to a credit institution.
For example, if an IP address logs in from a certain geographic region, but the timezone does not match, it may be considered a fraud indicator.
Regarding the browser, suspicion may arise from unusual configurations, using multiple browsers within a short time, etc.
#5. Blacklist and known fraud IP checks
If an IP address is associated with known fraud cases or is blacklisted, it is a direct reason to flag the applicant as suspicious.
The role of IP intelligence in credit risk scoring
By incorporating IP risk management into credit scoring processes, lenders can benefit in several ways:
1. Enhancing identity verification reliability. Analyzing an applicant's IP address helps establish their real location and compare it with the data provided in the application.
Any discrepancies detected will indicate fraudulent activity.
2. Detecting high-risk behavior. Lenders can identify transactions from suspicious IP addresses, such as datacenter IPs or flagged regions.
Additionally, lenders can detect multiple loan applications submitted from the same IP address.
3. Improving the accuracy of credit application decisions. Research shows that using alternative data for lending organizations (including IP lookup data) combined with traditional data provides maximum efficiency:
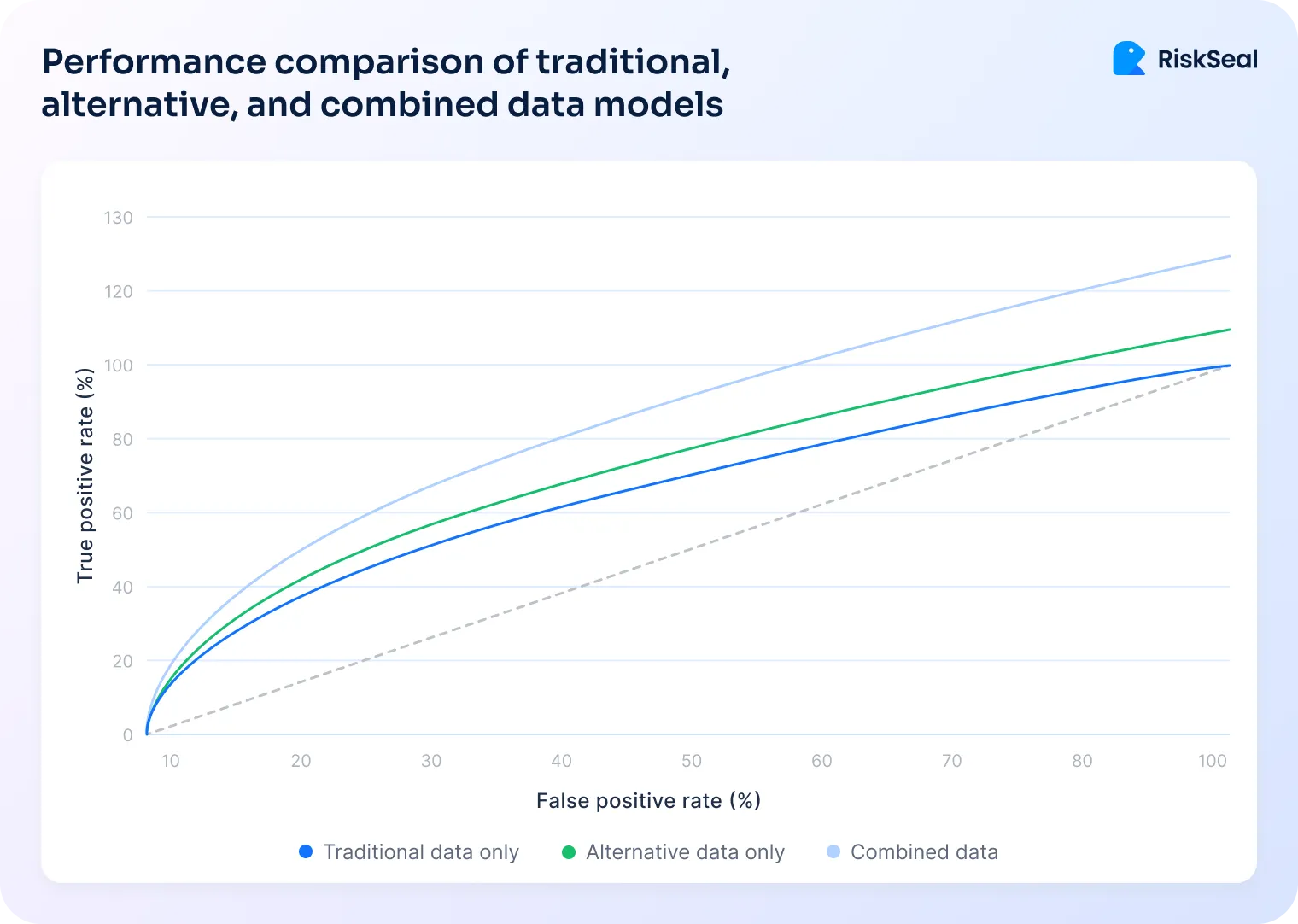
Also, assigning risk scores based on behavioral anomalies helps make informed decisions. For example, submitting multiple applications from different locations can be considered a risk factor.
4. Preventing synthetic identity fraud. IP address location lookup helps detect automated bots and attempts to create fake loan applications.
The use of VPNs or other anonymization services to hide the real location is a strong fraud indicator.
Implementing IP-based risk detection in credit risk workflows
The integration of IP lookup for global risk insights occurs in several stages.
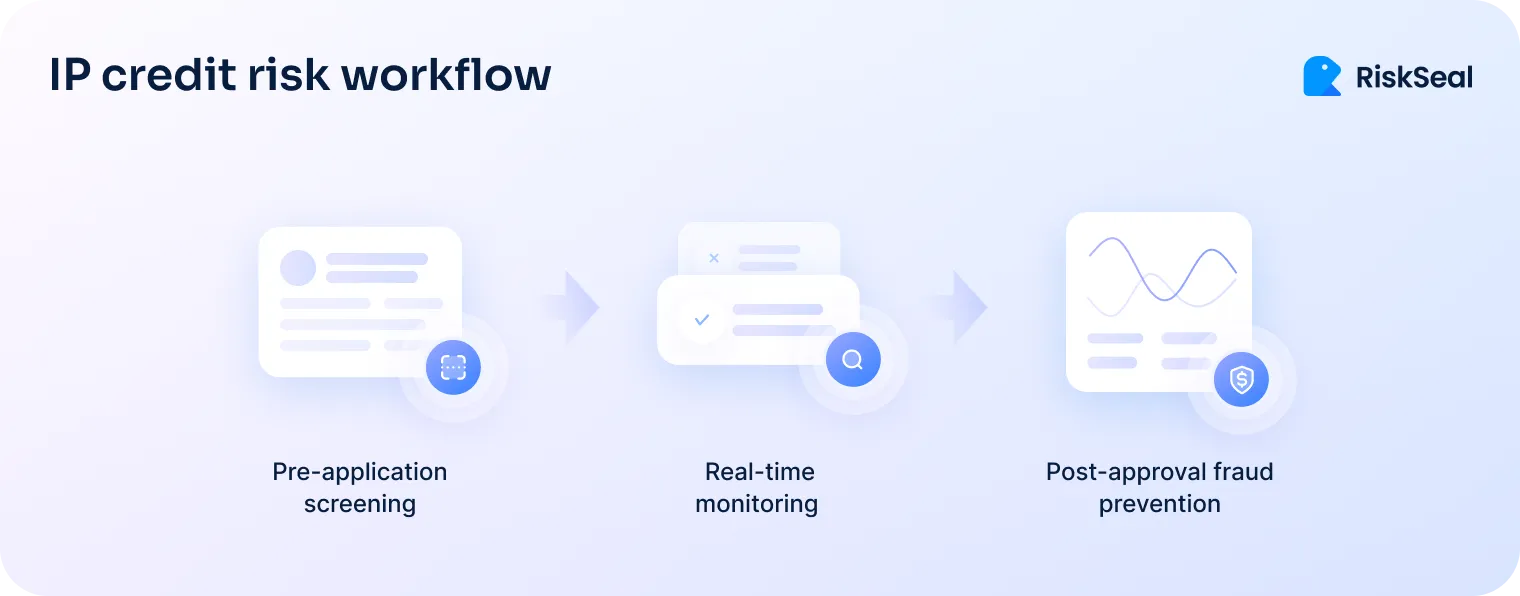
Step #1. Pre-application screening
This involves checking the IP address at the time of loan application submission. This allows lenders to flag suspicious applicants before a full review begins.
Key risk indicators at this stage:
- Geolocation mismatches
- Use of proxies or VPNs
- Known blacklisted IPs
- Multiple applications from a single IP
For example, RiskSeal clients filter out up to 70% of high-risk applications at this early stage.
Step #2. Real-time monitoring during underwriting
If an application passes the initial screening, the underwriting process begins. Here, IP address lookup plays a crucial role in risk assessment.
Key IP analysis techniques include:
- Behavioral analysis
- Device fingerprinting correlation
- Time-zone inconsistencies
- Velocity tracking
Step #3. Post-approval fraud prevention
Even after a loan is approved, lending organizations must remain vigilant. Continuous account monitoring is essential for fraud prevention.
Key post-approval monitoring strategies:
- Login and transaction IP tracking
- Anomalous usage pattern detection
- IP address consistency checks
- Automated alerts for high-risk behavior
IP credit insights with RiskSeal
RiskSeal Digital Credit Scoring system helps lenders enhance risk assessment through data enrichment.
Among other factors, analyzing a potential borrower's IP address plays a significant role.
This provides lenders with several advantages:
Geolocation verification. We compare the borrower’s actual location with the information provided in the application. Discrepancies indicate potential fraud.
Detection of anonymity tools. Identifying the use of VPNs, proxy servers, or TOR networks should alert lenders, as many fraudsters rely on anonymizers to execute their schemes.
IP address type analysis. We determine whether an IP address is residential, mobile, or associated with data centers and assign a risk level accordingly.
Blacklist screening. If an IP address is linked to phishing, spam, or data theft, it is a clear warning for credit organizations about the borrower's high-risk level.
Thanks to these features, RiskSeal enables lending institutions to make more informed credit decisions, reduce fraud rates, and tailor financial products to borrowers' individual needs.

The 2026 guide to LATAM digital footprints for credit scoring
Inside the LATAM alternative credit data report





FAQ
See more
Dive into explainable AI in credit scoring to boost transparency, reduce bias, build trust, and ensure full regulatory compliance.

Learn how IP address analysis can enhance borrower creditworthiness assessments.

Examine how to integrate location insights into your credit scoring models to reduce default rates and gain a competitive advantage.


.svg)

.webp)
.webp)

